
Share :
Introduction
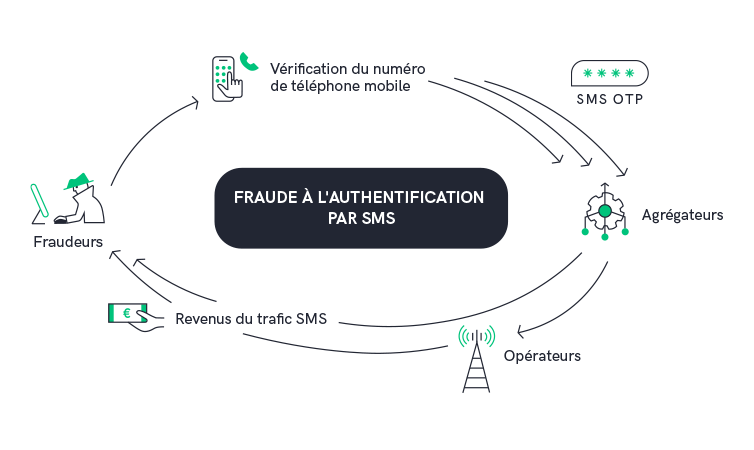
A new type of fraud is gaining ground for web services that use SMS OTP identity verification. It's called " SMS PUMPING" or "Artificially Inflated Traffic". Fraudsters generate large volumes of SMS from mobile applications or websites, by sending massive verification codes. According to a study by Mobilesquared, this fraud accounted for more than 20% of global business SMS traffic in 2022. Find out how you can protect yourself from this type of fraud and how smsmode© can help.
How does SMS Pumping work?
Fraudsters use various methods, including bots, to generate false requests via SMS. For example, they create fake accounts on an application or website, request password updates, click on "forgot password", etc. They take advantage of the presence of a telephone number input field to receive a one-time access code (OTP ), a download link or any other type of content delivered by SMS. If this verification form is not monitored, fraudsters can exploit it to generate fraudulent SMS traffic from your account.
In the majority of cases, attackers use their bot to mass-fill a field or form to "validate" these fake accounts, which triggers the sending of an SMS.
The SMS are sent to numbers over which the fraudsters have "control", enabling them to obtain a share of the revenues generated by this Artificially Inflated Traffic ( SMS ).
If you suffer such an attack, as the owner of the application, you will probably be forced to pay the bill for message delivery. The aim of this fraud is to make money, not to steal information.
There are two ways to make a profit with this type of fraud:
Case n°1
Fraudsters benefit from a partner operator/aggregator, with whom they have concluded a revenue-sharing agreement. They generate massive shipments of SMS to these operators, and divide the revenues among themselves.
Case n°2
An operator/aggregator is unknowingly exploited by the fraudsters.
In the second case, small operators or aggregators are paid by larger players for the volume of traffic they can allow to pass through. A fraudster can therefore create a fake company and promise a large amount of traffic (which he will make himself). The small operator/aggregator may not seek to know the source of the traffic and ends up supporting the fraud.
As you can see, in both cases, this type of fraud is more likely to occur among smaller operators. It's also common for these traffic anomalies to originate from far-flung destinations , as some international destinations have higher delivery costs and are therefore more profitable for fraudsters (and more costly for victim companies).
But businesses aren't the only losers in this story. OTP authentication fraud is a problem for the entire messaging ecosystem.
Operators and aggregators can hardly take action without the validation of their customers, which reduces the scope of action against this fraud and leads to a loss of credibility as well as a legitimate frustration for their impacted customers.
How to determine if you are a victim of an attack?
This fraud can go completely undetected, only becoming apparent after comparing the volume of messages delivered with the number of actual authentications.
However, there are a number of things that can tip you off:
- A peak of messages sent to adjacent numbers (e.g. +33611111110, +33611111111, +33611111112, +33611111113, etc.) and therefore controlled by the same mobile network operator.
- A large number of unsuccessful verification cycles (conversion rate down sharply)
- A large volume of SMS sent to destinations where you have little or no presence.
What actions can be taken to protect yourself?
Although there is no miracle protection against this new type of fraud, companies can implement a few good prevention and detection practices that can significantly reduce these attacks. Involving customers is key to effectively combating fraudNo vendor-side solution can guarantee 100% effectiveness against these attacks. smsmode© can support you in implementing these best practices, and also provide a range of features to drastically limit fraud.
Two-factor authentication (2FA) via SMS has become a widespread way of improving security. However, these SMS 2FA must be optimized, and your supplier must guarantee a high level of security.

IP control
Add additional checks on IP, user or device identifiers when a new user creates an account (ISP/proxy/TOR/cloud provider, etc.). This allows you to identify suspicious behavior and take action before the fraudster requests that a message be sent.
You can also limit the number of SMS request attempts from the same IP address or device and include a latency in the requests, e.g. one password reset per hour, etc.
VPN monitoring and detection
While there are legitimate use cases for VPNs, attackers will surely use one, if only to circumvent an IP address block. There are many solutions for VPN detection.
Detecting bots
Fraudsters are likely to use bots to generate large volumes of SMS. Using a feature like CAPTCHA can help detect and prevent bots from repeating requests.
Set up a "pre-audit" system
Avoid making SMS your first and only authentication device. This type of process certainly adds a step to creation and therefore a little friction for legitimate users, but can deter automated scripts and bots. For example, you can ensure that your users confirm their e-mail address before their telephone number.
Set server limits and service rates
Ensure that your application will not send more than one message every X seconds to the same mobile number range or prefix. Set up throughput limits per user, IP or device ID.
You can set up rules that restrict the number of requests allowed from a specific IP address or user over a given period by implementing modules in your web server such as Nginx and Apache to limit the rate or frequency of requests to your server.
Set sending limits
You can set several types of limits in collaboration with your smsmode© account manager:
- Monthly limits to prevent overbilling
- Daily limits to add a layer of monitoring. smsmode© will send you alerts for each level crossed.
- A limit on the number of SMS sent per minute for prevention purposes.
Establish exponential delays between audit attempts
Setting exponential delays between requests made with the same phone number is an effective way of preventing mass mailing. They may not prevent fraud, but they can slow attackers down enough for them to decide it's not worth attacking your application.
Implement geographic permissions to restrict destination countries
Review the geographical zones in which authentication on your application is possible, and disable all destinations not eligible for your services (most cases occur in countries where brands are not present).
You can also create a list of automatic authorizations or blocks based on the phone number's country code.
Check phone number before sending with smsmode©
Use our API Lookup to obtain all information on the phone number used for authentication (country code, type of number, network, etc.).
You can also automate this API request. Lookup can help you identify the operator(s) responsible for excessive traffic (knowingly or unknowingly), so you can block them.
Monitor unique access code (OTP) conversion rates and create alerts
Create an alert in your internal monitoring tool for the authentication conversion rate (i.e., number of OTP validated by end users / number of OTP sent). If you notice that this rate starts to drop abnormally, especially if the OTP requests come from an unexpected country, trigger an alert for a manual review.
An analysis of the DLRs received from smsmode© may enable you to block the service if you suspect one or more numbers.
What should you do if you suspect fraud on your smsmode account?
Send an e-mail to smsmode
with the following details:
Account ID:
Channel(s) concerned:
Date and time range:
Destination countries SMS :
Business Description:
Try out our SMS platform and benefit from 20 free test credits, with no obligation.
